Configuring Active Directory To Support Kerberos For Mac
Introduction – Kerberos SSO. Foldr can be configured to authenticate users using Kerberos authentication. This provides a convenient way to automatically sign users into Foldr if they are using a PC or Mac that is bound to Active Directory.
Directory Utility User Guide
You can use the Active Directory connector (in the Services pane of Directory Utility) to configure your Mac to access basic user account information in an Active Directory domain of a Windows 2000 or later server.
The Active Directory connector generates all attributes required for macOS authentication from Active Directory user accounts. It also supports Active Directory authentication policies, including password changes, expirations, forced changes, and security options. Because the connector supports these features, you don’t need to make schema changes to the Active Directory domain to get basic user account information.
Note: macOS Sierra and later can’t join an Active Directory domain without a domain functional level of at least Windows Server 2008, unless you explicitly enable “weak crypto.” Even if the domain functional levels of all domains are 2008 or later, the administrator may need to explicitly specify each domain trust to use Kerberos AES encryption. See the Apple Support article Prepare for macOS Sierra 10.12 with Active Directory.
When macOS is fully integrated with Active Directory, users:
Are subject to the organization’s domain password policies
Use the same credentials to authenticate and gain authorization to secured resources
Are issued user and machine certificate identities from an Active Directory Certificate Services server
Can automatically traverse a Distributed File System (DFS) namespace and mount the appropriate underlying Server Message Block (SMB) server
Tip: Mac clients assume full read access to attributes that are added to the directory. Therefore, it might be necessary to change the ACL of those attributes to permit computer groups to read these added attributes.
In addition to supporting authentication policies, the Active Directory connector also supports the following:
Packet encryption and packet-signing options for all Windows Active Directory domains: This functionality is on by default as “allow.” You can change the default setting to disabled or required by using the
dsconfigadcommand. The packet encryption and packet signing options ensure all data to and from the Active Directory domain for record lookups is protected.Dynamic generation of unique IDs: The controller generates a unique user ID and a primary group ID based on the user account’s globally unique ID (GUID) in the Active Directory domain. The generated user ID and primary group ID are the same for each user account, even if the account is used to log in to different Mac computers. See Map the group ID, Primary GID, and UID to an Active Directory attribute.
Active Directory replication and failover: The Active Directory connector discovers multiple domain controllers and determines the closest one. If a domain controller becomes unavailable, the connector uses another nearby domain controller.
Discovery of all domains in an Active Directory forest:Gmt version 5 download. You can configure the connector to permit users from any domain in the forest to authenticate on a Mac computer. Alternatively, you can permit only specific domains to be authenticated on the client. See Control authentication from all domains in the Active Directory forest.
Mounting of Windows home folders: When someone logs in to a Mac using an Active Directory user account, the Active Directory connector can mount the Windows network home folder specified in the Active Directory user account as the user’s home folder. You can specify whether to use the network home specified by Active Directory’s standard home directory attribute or by the home directory attribute of macOS (if the Active Directory schema is extended to include it).
Using a local home folder on the Mac: You can configure the connector to create a local home folder on the startup volume of the Mac. In this case, the connector also mounts the user’s Windows network home folder (specified in the Active Directory user account) as a network volume, like a share point. Using the Finder, the user can then copy files between the Windows home folder network volume and the local Mac home folder.
Creation of mobile accounts for users: A mobile account has a local home folder on the startup volume of the Mac. (The user also has a network home folder as specified in the user’s Active Directory account.) See Set up mobile user accounts.
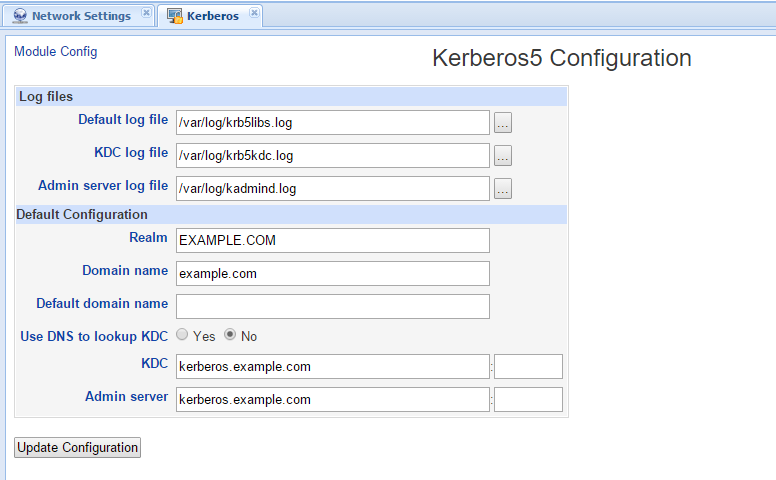
LDAP for access and Kerberos for authentication: The Active Directory connector does not use Microsoft’s proprietary Active Directory Services Interface (ADSI) to get directory or authentication services.
Detection of and access to extended schema: If the Active Directory schema has been extended to include macOS record types (object classes) and attributes, the Active Directory connector detects and accesses them. For example, the Active Directory schema could be changed using Windows administration tools to include macOS managed client attributes. This schema change enables the Active Directory connector to support managed client settings made using macOS Server.